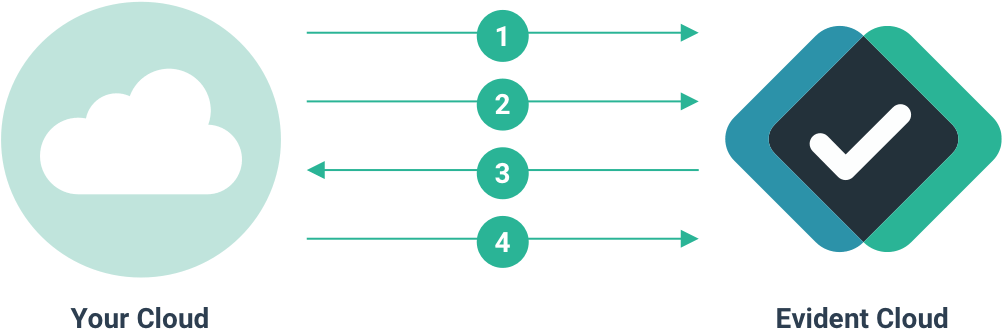
Create a request with VerifyAPI
VerifyAPI is a RESTful JSON API that allows you to create a request for verification, and retrieve information about an existing request.
You will need your username and an API key to authenticate yourself with VerifyAPI using HTTP Basic Auth. If you did not receive your credentials as you signed up, please send an email to support@evidentid.com. You should have one API key for production use, and another API key for sandbox use. We will show you how to use an API key with the corresponding VerifyAPI instance.
- The production VerifyAPI is located at
https://verify.api.evidentid.com/api/v1
- The sandbox VerifyAPI is located at
https://verify.api.demo.evidentid.com/api/v1
When presenting example calls like the one shown here, we will refer to your selected API as $VERIFY and your account name as $ACCOUNT.
Your API keys are secrets! You should call VerifyAPI endpoints from your server, and only your server. Be mindful of any leaks in how your key is used to ensure maximum protection.
For this integration, we create a request to verify information belonging to the end-user with the email jon.doe@somedomain.com. A verification request consists of attributes, which are small, verifiable data items used to build your own report of what you expect to be verified. The end-user will need to authenticate and submit personal data to the system for verification. Once the request is created, the end-user has 28 days from the time of their last submission to finish before the overall request times out.
To get more VerifyAPI examples please download our Postman collections from GitHub.
| Field |
Description |
email |
The email belonging to the user that owns the personal data you wish to verify. Depending on the integration mode, the user may be sent an email instructing them to answer a verification request. |
summary |
This is a short summary of the verification request and will show up in the subject line of the emails sent out to your users |
description |
A string that describes the intent of the verification request. This is used for your own records or communications with the end-user where applicable. |
userAuthenticationType |
This field controls how the end-user should authenticate with the system. For this integration mode, set this to blindtrust. |
attributesRequested |
An array of objects with key attributeType designating the data items you wish to verify. |
$ curl "$VERIFY/verify/requests" \
-X POST \
--header "Content-Type: application/json" \
-u "$ACCOUNT" \
-d @- << EOF
{
"email": "jon.doe@somedomain.com",
"summary": "Please provide your ServSafe certificate number",
"description": "To continue with your account creation please provide your ServSafe certificate number. We've partnered with Evident ID who will verify your credentials on our behalf.",
"userAuthenticationType": "blindtrust",
"attributesRequested": [
{"attributeType": "certifications.servsafe.servsafe_food_handler.valid"}
]
}
EOF
Enter host password for user "$ACCOUNT": # Paste API key here to keep it out of history.